$4 Million, 8 Zero-Days, One Traitor: How a Defense Contractor Sold America's Cyber Weapons to Russia
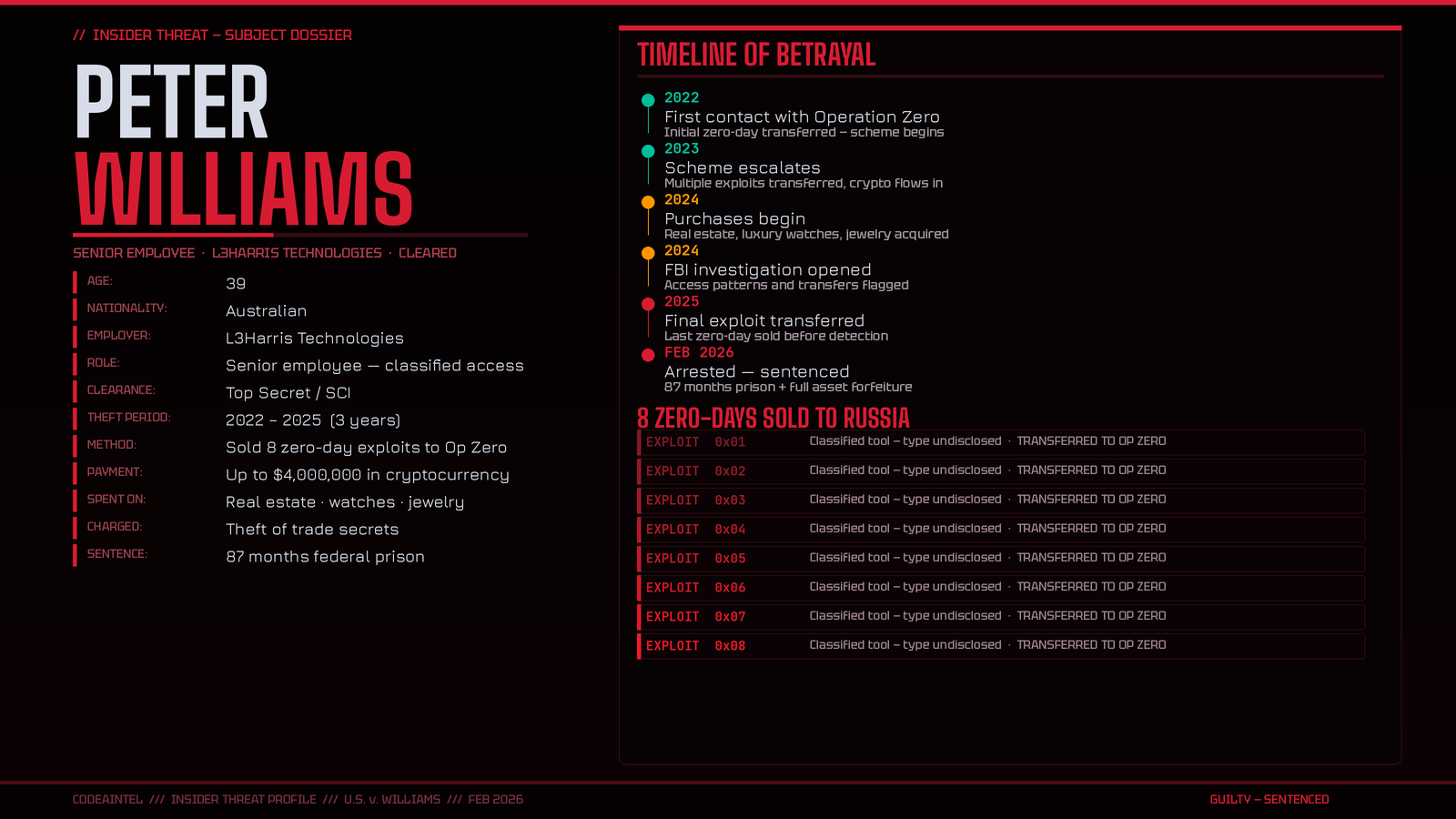
Peter Williams didn't hack anything. He didn't need to. He already had the keys — and he auctioned them off to the highest bidder wearing a Russian flag.
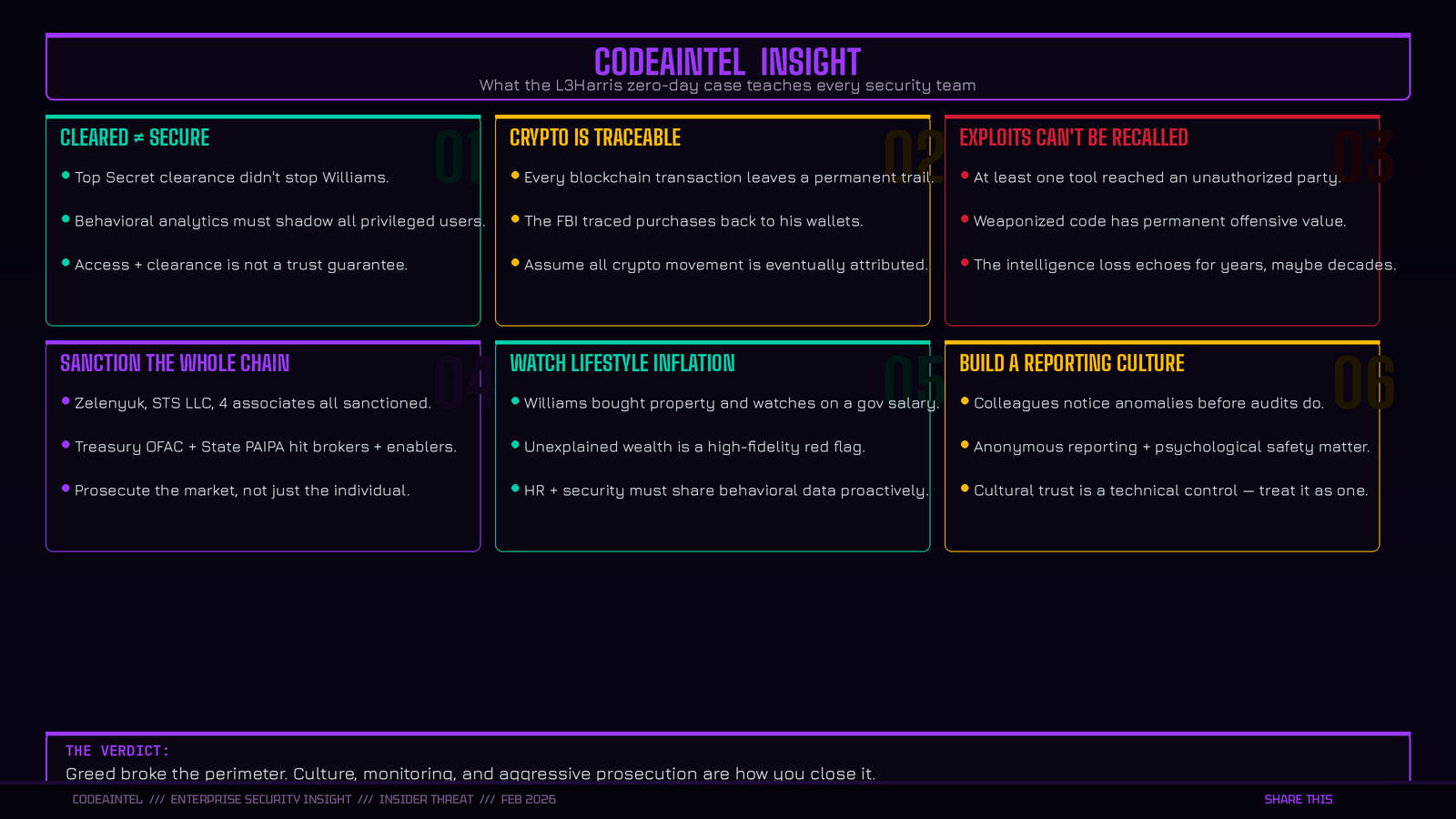
There is a category of threat that keeps national security officials awake at night — not the nation-state hacker probing systems from a Moscow apartment, but the cleared insider who walks through the front door every morning, past the badge reader, into the vault. Peter Williams was that threat.
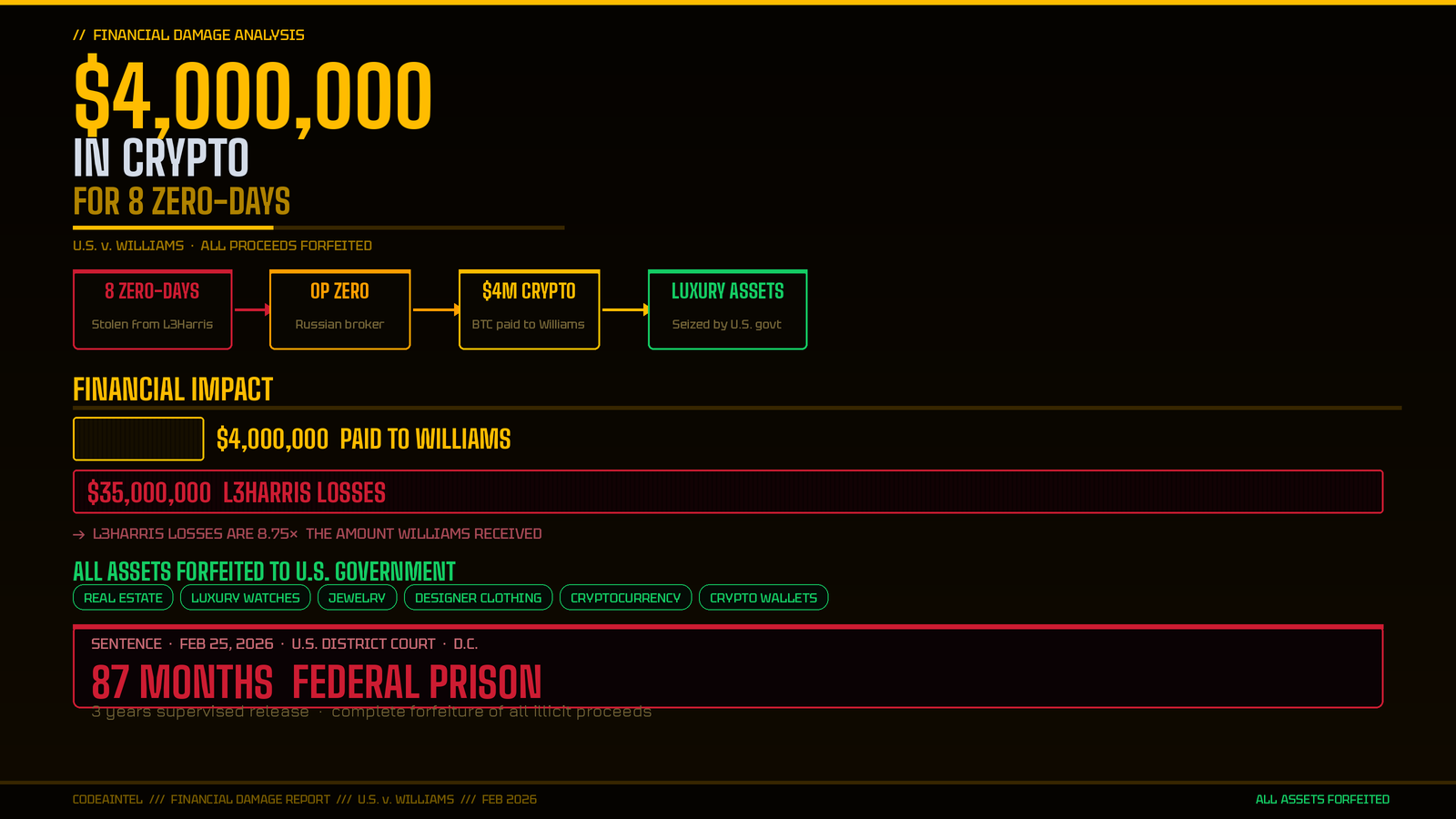
A 39-year-old Australian national and former senior employee at L3Harris — one of the United States’ premier defense technology contractors — Williams has been sentenced to 87 months in federal prison for selling eight zero-day exploits to Operation Zero, a Russian exploit broker, over a three-year period between 2022 and 2025. The price: up to $4 million in cryptocurrency, spent on properties, luxury watches, clothing, and jewelry.
The tools he sold were not his to sell. They were developed exclusively for the U.S. government and select allies. And according to the DOJ sentencing memorandum, they were capable of being “used against any manner of victim, civilian or military around the world” — enabling everything from ransomware to “state directed spying and offensive cyber operations against military targets.”
He didn’t steal a spreadsheet. He sold the cyber equivalent of a loaded gun pointed at millions of devices — and handed it to Russia.
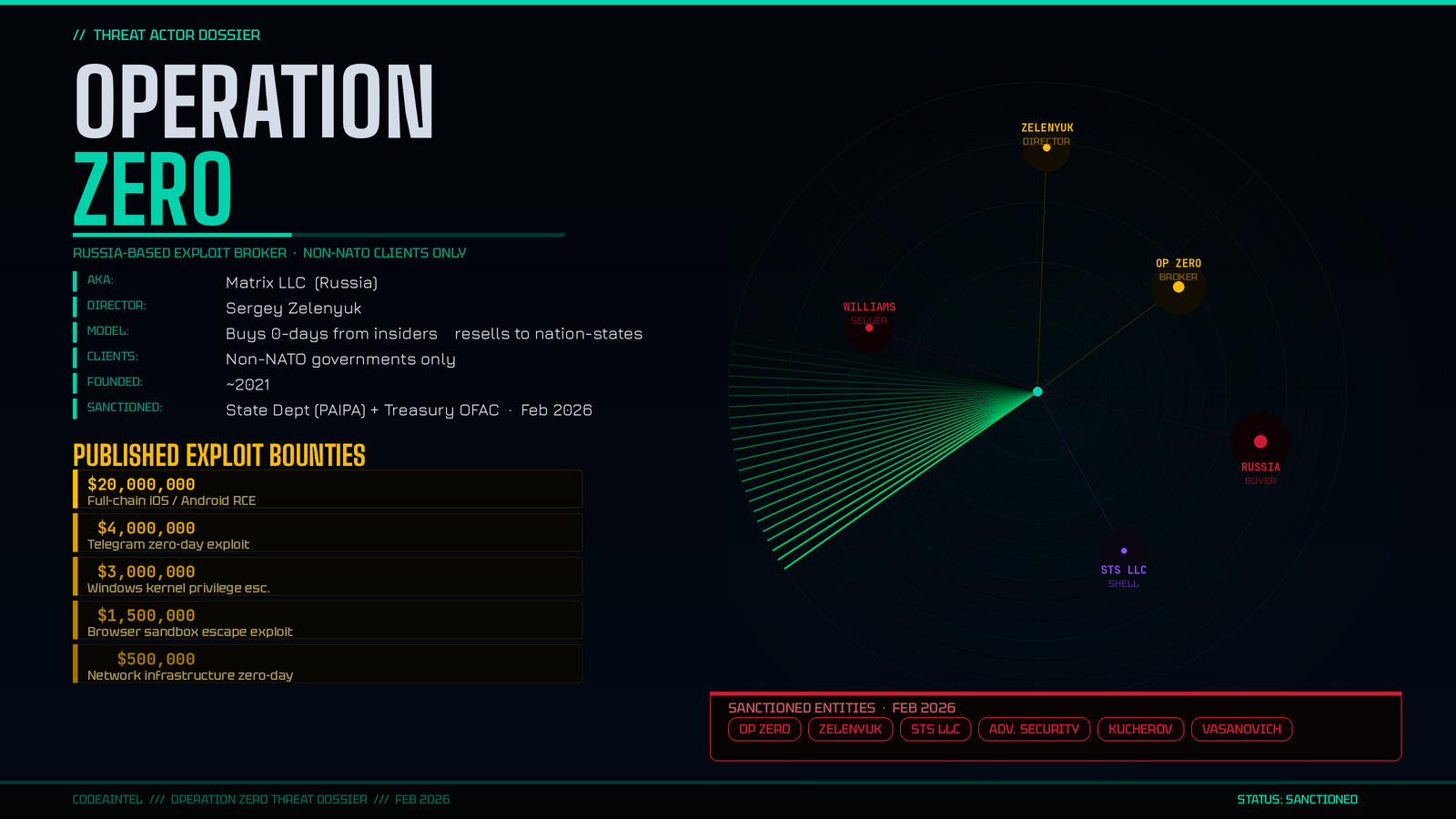
Who Is Operation Zero?
Operation Zero — now officially sanctioned by both the U.S. State Department and Treasury’s OFAC — is not a shadowy dark-web forum. It is a structured, commercially operating exploit brokerage based in Russia, run by Sergey Sergeyevich Zelenyuk, who also created a parallel entity called Special Technology Services LLC (STS) registered in the UAE — almost certainly to circumvent sanctions on Russian banking.
The numbers on Operation Zero’s published bounty board tell you everything about who their customers are:
$4 million for Telegram exploits
$20 million for full-chain Android or iPhone remote code execution
These are not bug bounty prices. These are nation-state prices. Zelenyuk has openly stated Operation Zero sells exclusively to non-NATO countries — a business model that is, in plain terms, the commercialization of offensive cyber capability for foreign intelligence services.
The Treasury has now sanctioned Zelenyuk, Operation Zero, STS, and four associated individuals and entities — including Oleg Kucherov, suspected of TrickBot gang membership, and Azizjon Mamashoyev, who ran a parallel exploit brokerage called Advance Security Solutions offering bounties for U.S.-built software vulnerabilities.
At least one of the tools Williams sold has already been transferred to an unauthorized user.
The Scale of What Was Lost
L3Harris has quantified its losses at $35 million. That is the financial damage — the cost of rebuilding, revoking, and replacing eight compromised exploit tools that were supposed to be among the U.S. government’s most closely held offensive capabilities.
The true cost cannot be measured in dollars. Zero-day exploits developed for national defense represent years of research, sophisticated vulnerability discovery, and controlled operational security. Once sold, they cannot be unsold. Once in Russian hands, they can be:
Repurposed for espionage operations against U.S. allies
Analyzed to understand how U.S. offensive capabilities work and how to defend against them
Resold to additional state actors — Operation Zero’s business model is brokerage, not exclusivity
Williams didn’t just betray his employer. He inverted his entire professional purpose. These tools existed to protect — and he converted them into weapons for sale.
The Sanctions Web
The U.S. State Department’s designation of Operation Zero under the Protecting American Intellectual Property Act (PAIPA) and Treasury’s OFAC sanctions represent a coordinated whole-of-government response that goes beyond the criminal prosecution. The message is structural: not just “we jailed the seller,” but “we are dismantling the buyer.”
The sanctions freeze assets, block transactions, and expose anyone doing business with Operation Zero to secondary sanctions risk. The UAE-based STS entity being included in the designation signals that the U.S. is willing to pursue the sanctions evasion infrastructure, not just the primary actors.
Source: U.S. Department of Justice - https://www.courtlistener.com/docket/71644575/united-states-v-williams/