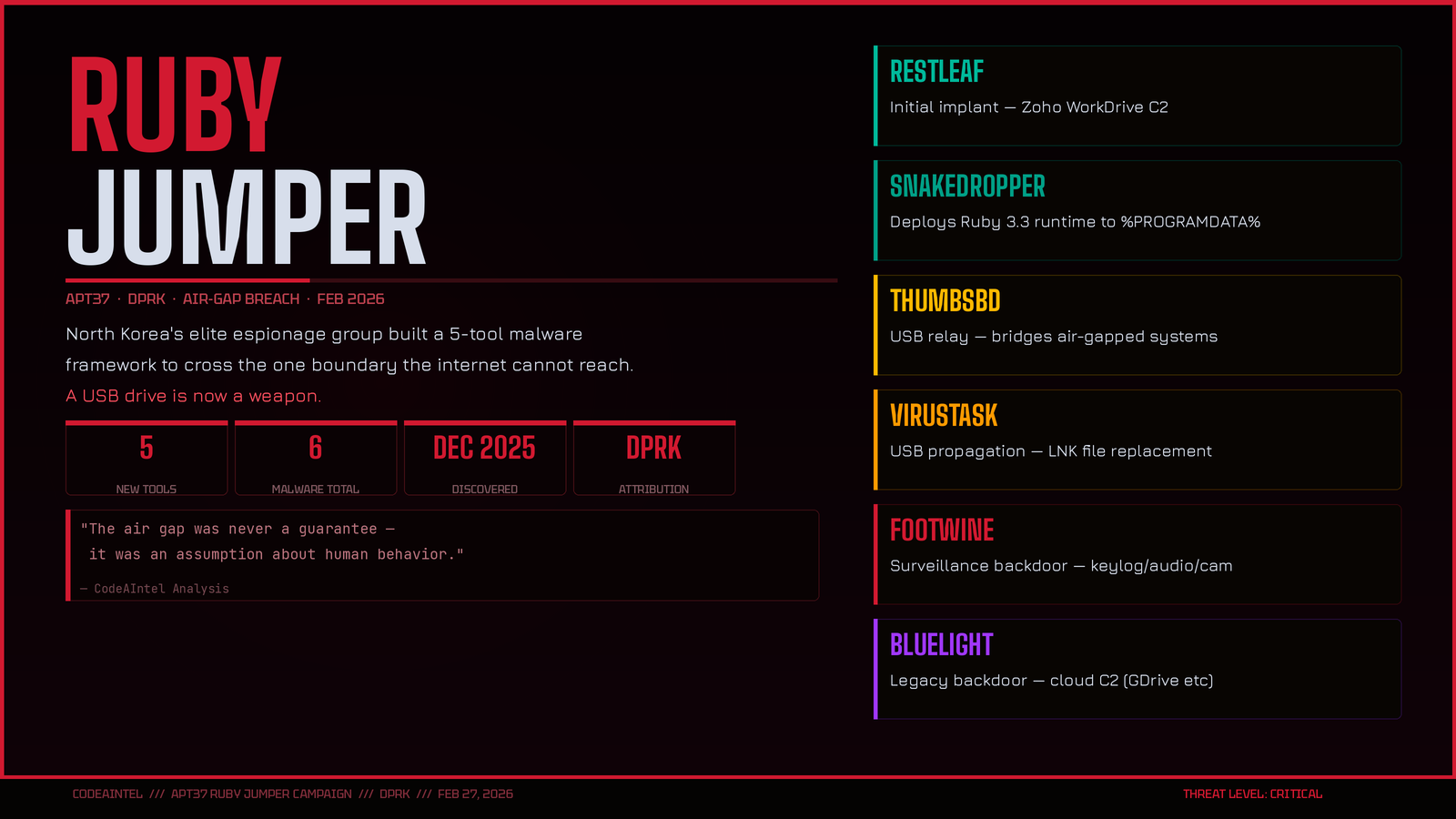
APT37's "Ruby Jumper" Uses USB Drives to Breach Networks That Were Never Online
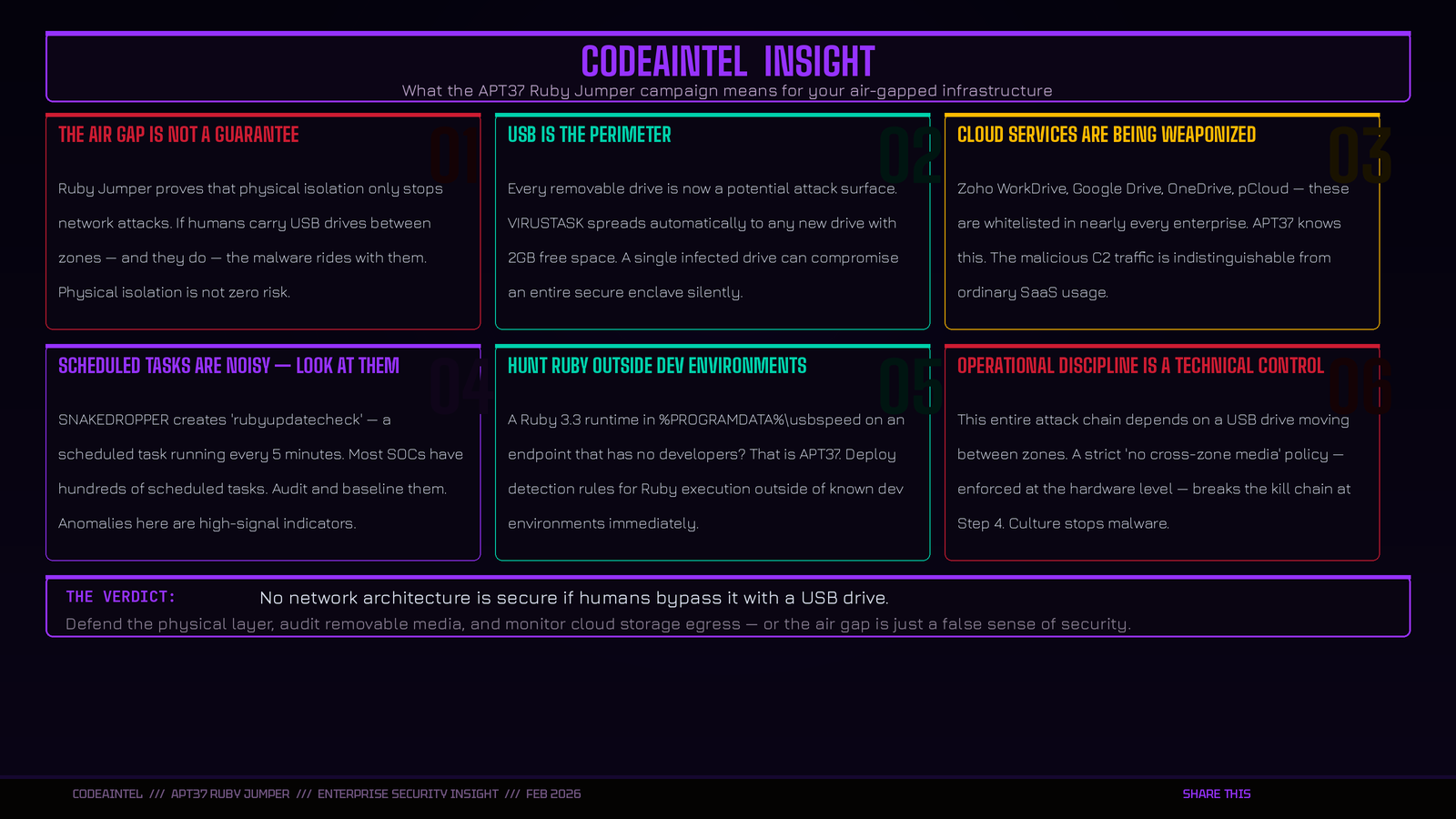
North Korea's elite hacking group built a five-tool malware framework specifically engineered to cross the one boundary the internet can't reach — the physical air gap. A USB drive is now a weapon.
What Happened
In December 2025, Zscaler ThreatLabz uncovered a new campaign by APT37 — the DPRK-backed espionage group also known as ScarCruft, Ruby Sleet, and Velvet Chollima. The campaign, named Ruby Jumper, introduces five previously undocumented malware tools designed to do one thing: move data and commands between internet-connected machines and systems that have never touched a network.
Air-gapped computers — the kind used in military installations, nuclear facilities, classified R&D labs, and critical infrastructure — are isolated at the hardware level. No Wi-Fi. No Ethernet. No Bluetooth. The only way in has always been physical. APT37 built an entire automated toolkit around that fact.
The result is a fully operational framework that turns any shared USB drive into a covert two-way command channel — invisible to network monitoring tools, invisible to cloud security stacks, and nearly invisible to the users carrying the drive between machines.
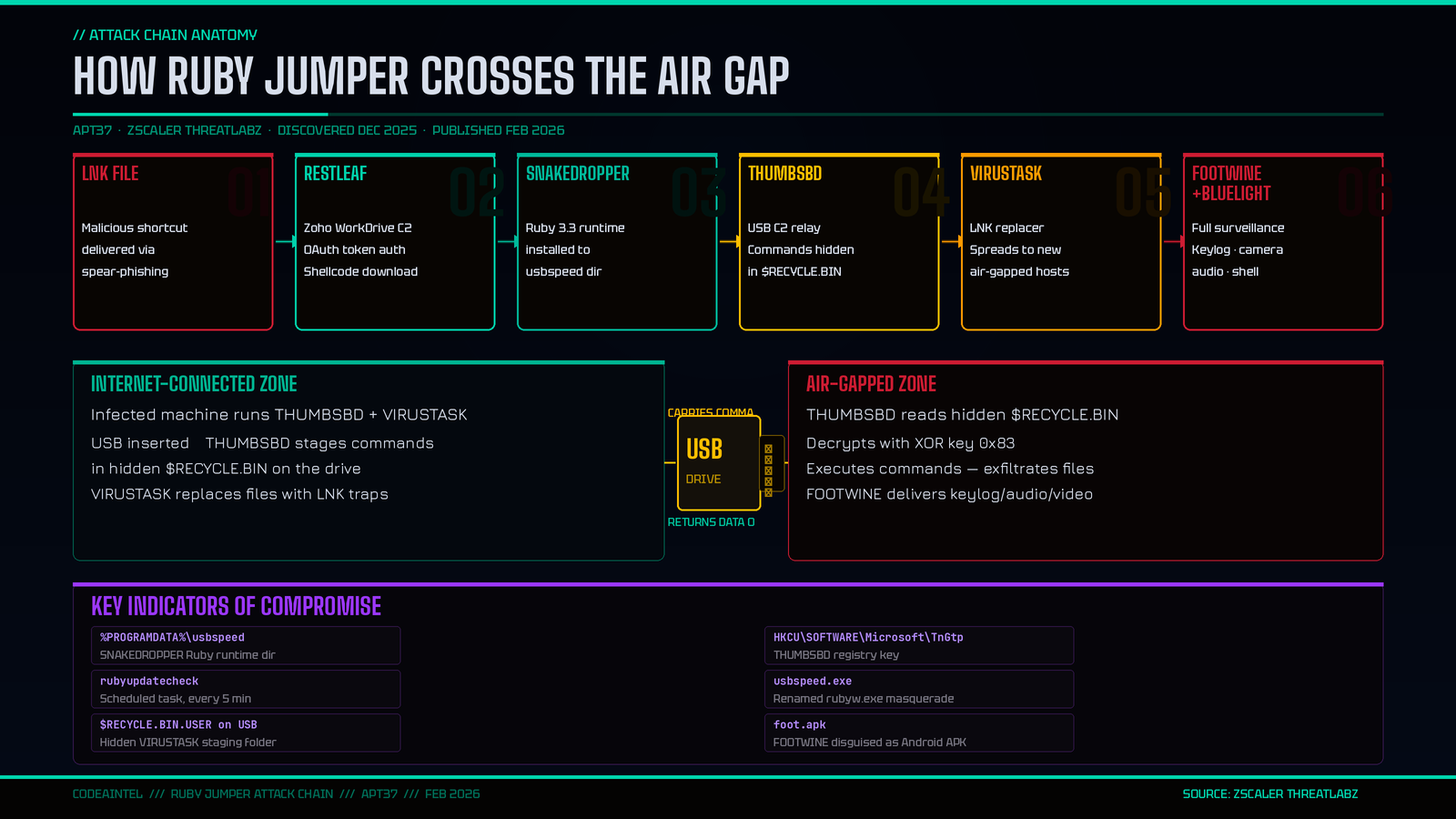
The Attack Chain
Stage 1 — Initial Access: The LNK File
The infection begins with a malicious Windows shortcut (.LNK) file, APT37’s signature entry vector. When opened, it silently launches PowerShell and a two-stage shellcode loader. Each stage decrypts the next using a single 1-byte XOR key, injecting code into a legitimate Windows system process to evade detection.
Stage 2 — RESTLEAF: The First Implant
RESTLEAF establishes the first foothold. It connects to Zoho WorkDrive — a legitimate cloud storage service — using hardcoded OAuth tokens to authenticate and pull further shellcode. This is the first documented instance of APT37 abusing Zoho’s platform. Because the traffic looks like routine SaaS usage, it blends seamlessly into enterprise environments. RESTLEAF creates timestamped “lion”-prefixed beacon files in a WorkDrive folder named “Second” to signal operator availability.
Stage 3 — SNAKEDROPPER: The Ruby Trojan
RESTLEAF loads SNAKEDROPPER, which silently installs a fully self-contained Ruby 3.3.0 runtime into %PROGRAMDATA%\usbspeed. The legitimate rubyw.exe binary is renamed to usbspeed.exe to masquerade as a USB utility. SNAKEDROPPER then:
Hijacks Ruby’s auto-loaded
operating_system.rbso malicious logic runs every time the interpreter startsEstablishes a scheduled task named
rubyupdatecheckthat fires every five minutes for persistenceDrops additional Ruby-named binaries that actually contain shellcode payloads
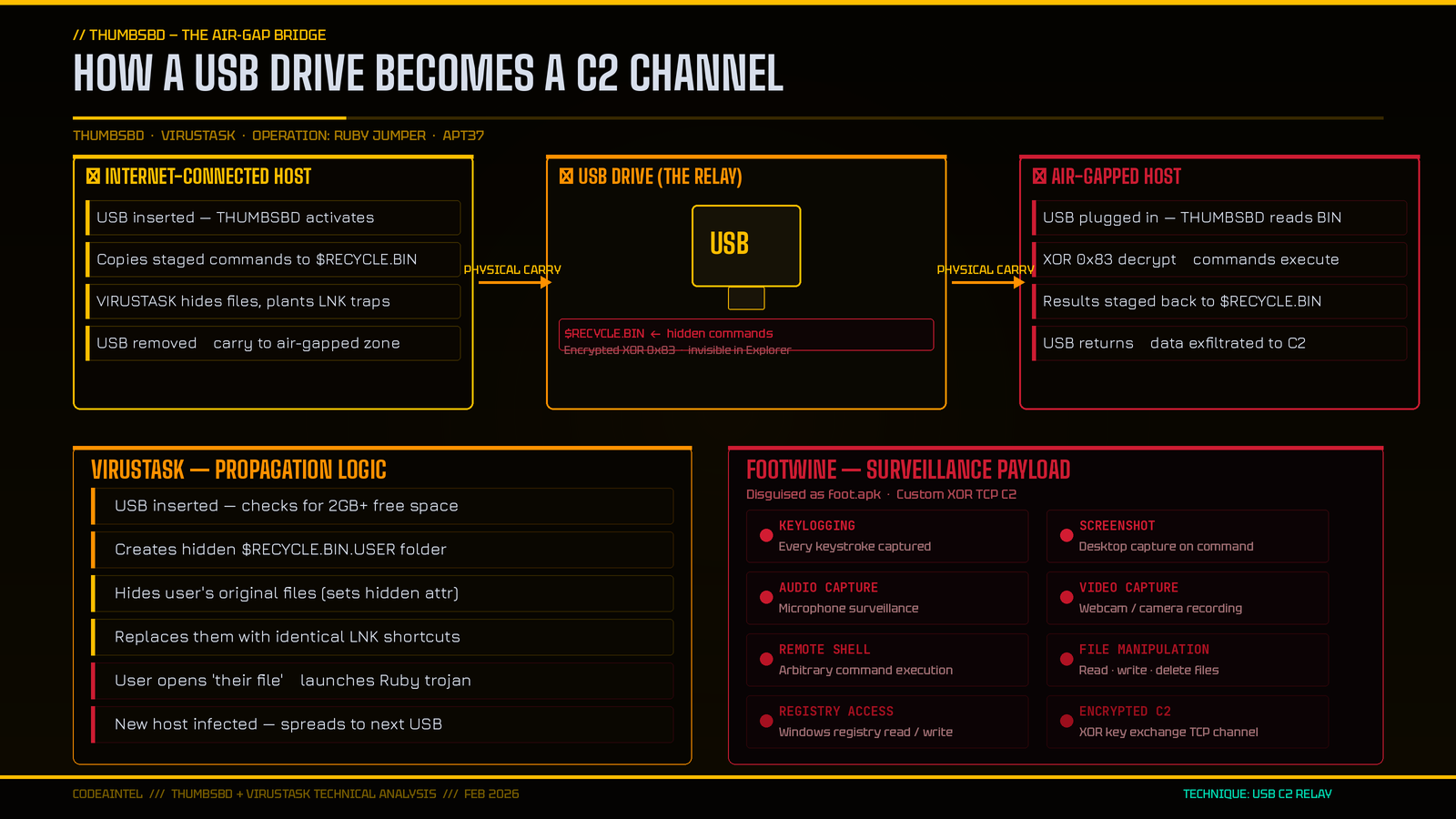
Stage 4 — THUMBSBD: The Air Gap Bridge
This is the operational centerpiece of Ruby Jumper. THUMBSBD acts as a covert relay, using removable media as a bi-directional command channel between the infected internet-connected machine and any air-gapped system.
When a USB drive is inserted into the infected internet-facing machine, THUMBSBD copies staged command files into a hidden $RECYCLE.BIN directory on the drive — a location invisible under default Windows Explorer settings. When that same drive is plugged into an air-gapped machine (also running THUMBSBD), the implant:
Reads files from the hidden
$RECYCLE.BINDecrypts them using XOR key
0x83Executes the operator’s commands: file exfiltration, system reconnaissance, arbitrary execution
Stages results back into
$RECYCLE.BINon the drive
When the USB is returned to the internet-connected machine, THUMBSBD exfiltrates the results to the cloud C2. The USB drive has become a fully automated, human-unaware command-and-control relay.
Stage 5 — VIRUSTASK: The Spreader
VIRUSTASK ensures the infection doesn’t stop at one air-gapped machine. When removable media is inserted, it:
Checks for at least 2GB of free space before proceeding
Creates a hidden folder named
$RECYCLE.BIN.USERat the drive root (mimics Windows Recycle Bin, invisible by default)Hides all legitimate user files and replaces them with identically named LNK shortcuts
When an unsuspecting user on a new machine opens what they believe is their own file, they launch the Ruby runtime — infecting the new host
Stage 6 — FOOTWINE + BLUELIGHT: Full Surveillance
Once access is established, THUMBSBD delivers FOOTWINE — a Windows backdoor disguised as an Android APK (foot.apk). FOOTWINE provides full surveillance capability:
Keylogging
Screenshot capture
Audio and video recording (microphone + camera)
File and registry manipulation
Remote shell access
Encrypted C2 over a custom XOR-based TCP protocol
The older BLUELIGHT backdoor — a long-standing APT37 tool — also deploys here, using Google Drive, OneDrive, pCloud, and Backblaze as C2 channels. Its use confirmed Zscaler’s attribution to APT37.
Why This Is Different
Air gap attacks are not new. Stuxnet did it in 2010. What makes Ruby Jumper operationally significant is the automation and scale.
Most air gap attacks require a human insider to physically carry a compromised device. Ruby Jumper removes the human element from the relay. Any shared USB drive — carried by a well-intentioned IT staffer, a contractor, or an engineer transferring files for patching — becomes an automated C2 relay without the carrier ever knowing. The malware self-propagates to new air-gapped hosts through VIRUSTASK, meaning a single infected drive can compromise an entire secure enclave over time.
The choice of cloud services as C2 — Zoho, Google Drive, OneDrive — is equally deliberate. These are services that organizations actively whitelist. Blocking them would break business operations. APT37 is exploiting the operational dependency organizations have on legitimate SaaS platforms.
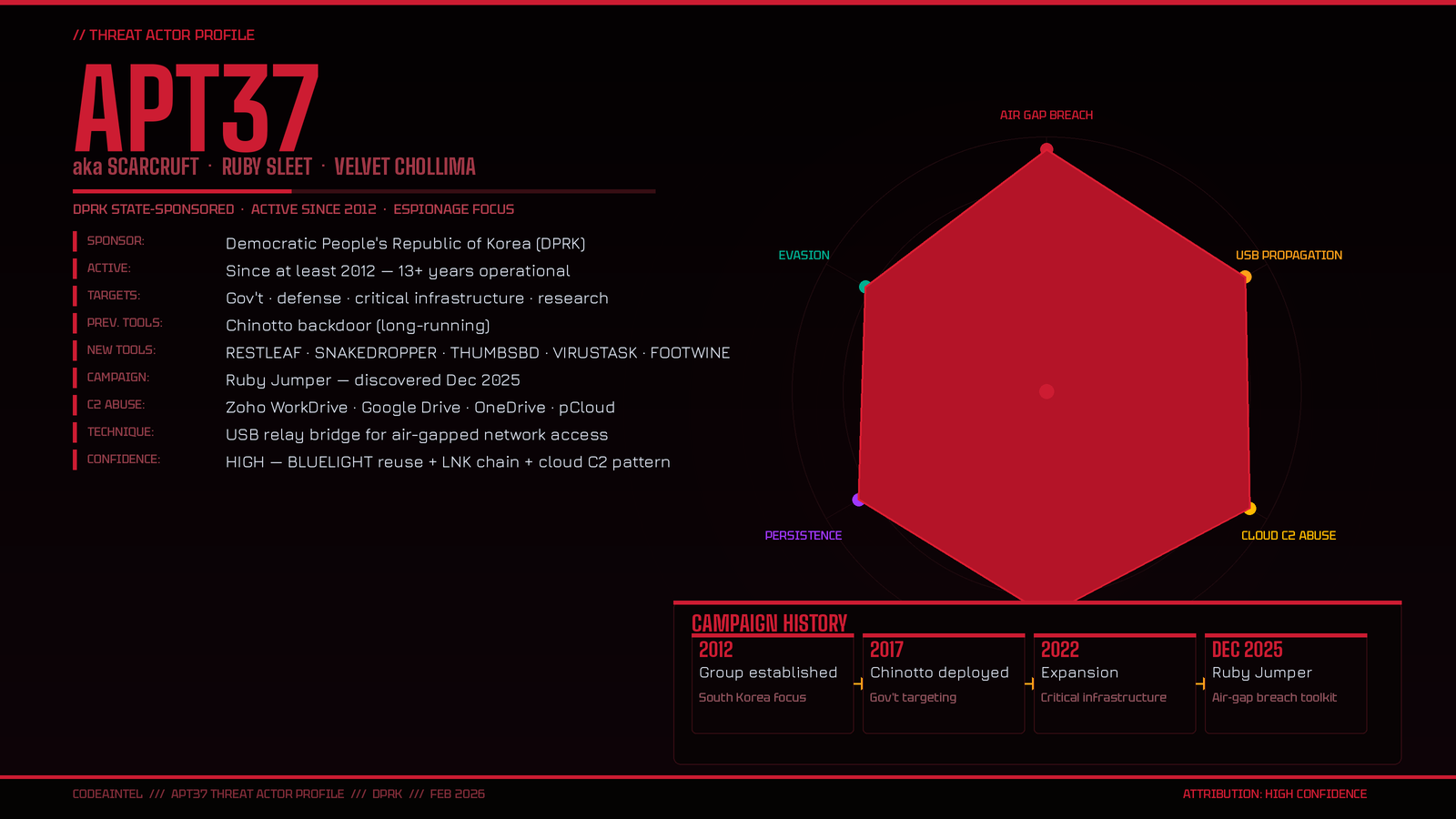
Who Is APT37?
APT37 (ScarCruft / Ruby Sleet / Velvet Chollima) is a DPRK state-sponsored cyber espionage group active since at least 2012. Historically focused on South Korean government entities, defense organizations, and individuals of interest to Pyongyang, the group has expanded its targeting to include critical infrastructure operators, research institutions, and international policy organizations.
Ruby Jumper represents a significant capability investment — the development of five entirely new malware tools, each engineered for a specific role in a complex multi-stage chain. This is not opportunistic crime. This is a deliberate, patient, state-funded operation targeting organizations that believed their air gap made them unreachable.
Indicators of Compromise
Certainly! Here is the list in a standard Markdown list format, with the indicators formatted as code blocks for easy individual copying:
Host Indicators
Indicator:
709d70239f1e9441e8e21fcacfdc5d08Filename: (None)
Description: Windows shortcut
Indicator:
ad556f4eb48e7dba6da14444dcce3170Filename: viewer.dat
Description: Binary (Shellcode+RESTLEAF)
Indicator:
098d697f29b94c11b52c51bfe8f9c47dFilename: (None)
Description: Binary (Shellcode+SNAKEDROPPER)
Indicator:
4214818d7cde26ebeb4f35bc2fc29adaFilename: ascii.rb
Description: Binary (Shellcode+ThmubsBD)
Indicator:
5c6ff601ccc75e76c2fc998o8d8cc9a9Filename: bundler_index_client.rb
Description: Binary (Shellcode+VIRUSTASK)
Indicator:
476bce9b9a387c5f39461d781e7e22b9Filename: foot.apk
Description: Binary (Shellcode+FOOTWINE)
Indicator:
585322a931a49f4e1d78fb0b3f3c6212Filename: footaaa.apk
Description: Binary (Shellcode+BLUELIGHT)
What To Do Now
For air-gapped / high-security environments:
Implement hardware-level USB port controls — restrict which devices can connect and to which systems
Enforce a clean USB policy: drives that touch internet-connected systems must never enter air-gapped environments without a sanitization workflow
Monitor for the
rubyupdatecheckscheduled task and audit all newly created scheduled tasksHunt for
%PROGRAMDATA%\usbspeedand hidden$RECYCLE.BIN.USERdirectories on endpoints and removable media
For all enterprise environments:
Audit cloud storage access from endpoints — Zoho WorkDrive, Google Drive, OneDrive, pCloud, Backblaze are all being abused as C2
Inspect LNK files in email attachments and downloaded content — APT37 consistently uses malicious shortcut files as the first entry point
Monitor for
usbspeed.exe, unusual Ruby runtime processes, andoperating_system.rbmodificationsBlock or alert on
HKCU\SOFTWARE\Microsoft\TnGtpregistry key creation
Source: Zscaler ThreatLabz